- Let's Connect!
- Email: support@securityboat.net
- Phone: +91 9175154999


JWT (JSON Web Token) is a widely used open standard for securely transmitting information between parties as a JSON object. It is commonly used for authentication and authorization purposes in web applications.
JWT consists of three parts: a header, a payload, and a signature.
In an algorithm confusion attack, attackers exploit a vulnerability by replacing one cryptographic algorithm with another in a security system. Their goal is to take advantage of weaknesses in the substituted algorithm to gain unauthorized access or elevate privileges within the system. By leveraging the system’s support for multiple algorithms, the attacker manipulates the algorithm selection process, compromising the system’s integrity and security.
In a JWT algorithm confusion attack, the attacker exploits the difference between symmetric (HS256) and asymmetric (RS256) cryptography used in JWTs. By changing the algorithm from RS256 to HS256, the attacker transitions from the use of a public-private key pair to a shared secret key. This enables the attacker to generate a signature using the shared secret key, which appears valid to the recipient. Unaware of the algorithm change, the recipient verifies the signature using the shared secret key, granting the attacker unauthorized access or elevated privileges within the system.
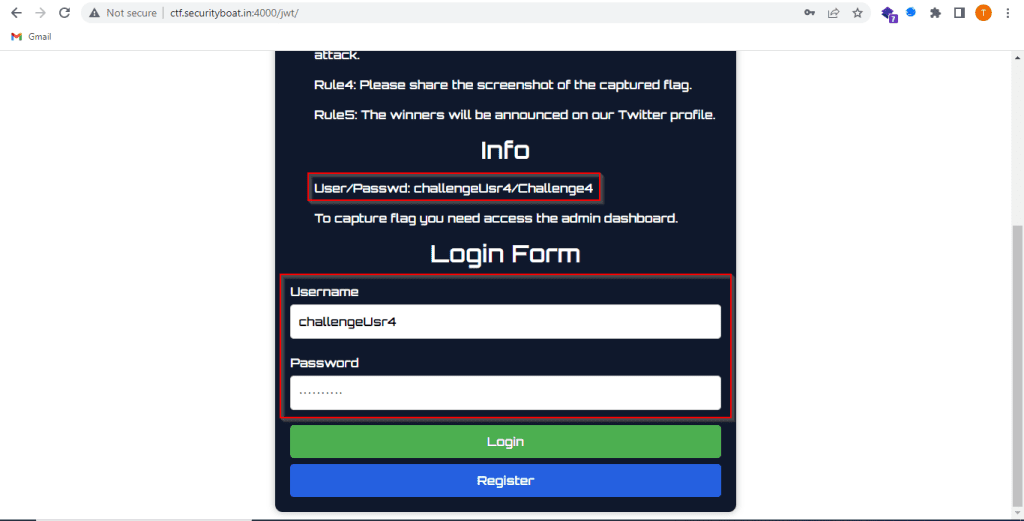
The aim of our challenge was to find the JSON Web Token vulnerability, which after exploitation, will display a hidden flag.
To begin, we first log in to the application using the provided credentials from the INFO section. Once we have logged in, we can verify that the home page is accessible, confirming a successful login.
We can observe that when we attempting to directly access the admin panel it results in an unauthorized access error message. This indicates that an alternative method is needed to gain access to the admin privileges. From this we also get a hint about the availability of admin panel using /admin.


Click on the Home link and intercept the request in the BurpSuite. By analyzing the intercepted request, we can identify that the application utilizes a JSON Web Token (JWT) for authorization. We can also observe that the RS256 algorithm is being employed for token signing, and the current user role assigned in the token is user.


Within the intercepted request, we can observe the user parameter in the GET request, change its value from “user” to admin. This modification is necessary because we want to impersonate an admin user and gain access to the admin panel.


Based on the information gathered, it becomes clear that an Algorithm Confusion attack can be utilized. The objective is to manipulate the algorithm from RS256 to a weaker algorithm, such as HS256. Within the intercepted request, change the algorithm parameter from RS256 to HS256. Additionally, we need to modify the role parameter from user to admin to acquire administrative privileges. JSON Web Token (JWT) extension of BurpSuite is utilized to modify the parameters. Similarly, another tool called “jwt tool” can be employed for the same purpose of manipulating the JWT parameters.


By forward the modified request using BurpSuite we can observe that the modified request is now successfully processed, and we are now logged in as an admin user, gaining access to the admin panel. But we still haven’t received the flag.


To access the flagged resource (in this case, the flag), navigate to the Users section. Repeat the process of algorithm confusion as described in steps 3 and 4. Modify the algorithm parameter to HS256 and the role to “admin” within the intercepted request. Once the modified request is forwarded, we can observe that the flag is accessible.


Use Strong and Resilient Algorithms
To mitigate the Algorithm Confusion vulnerability, it is crucial to use a strong and secure cryptographic algorithm for token signing and verification. Algorithms such as ES256 (ECDSA with SHA-256), EdDSA (Edwards-curve Digital Signature Algorithm), and RS256 (RSA with SHA-256) are all suitable options for signing JWTs. Avoid algorithms that are known to be vulnerable to algorithm confusion attacks. Specifically, ensure that you do not use weak algorithms like HS256. Instead, opt for stronger algorithms such as RS256, which rely on asymmetric key cryptography.
Validate Algorithm and Other JWT Parameters
Implement strict validation checks on the JWT parameters, including the algorithm. Validate that the algorithm used in the token matches the expected algorithm. Reject any tokens that contain unexpected or unsupported algorithms. This ensures that only authorized algorithms are accepted, preventing attackers from manipulating the algorithm parameter.
We always post such challenges. We also give rewards and shoutouts to winners of challenges. To participate in such challenges, follow us on Twitter, LinkedIn, and Instagram.
Our latest blogs and solution to challenges are available here.
We would like to express our gratitude for the valuable contributions made by other participants through their insightful write-ups. Below, you will find the references to these write-ups.